Litigation disclosure in the Business and Property Courts: a defensible eDiscovery workflow for disputes
Litigation disclosure in the Business and Property Courts: a defensible eDiscovery workflow for disputes
Workflow for disputes
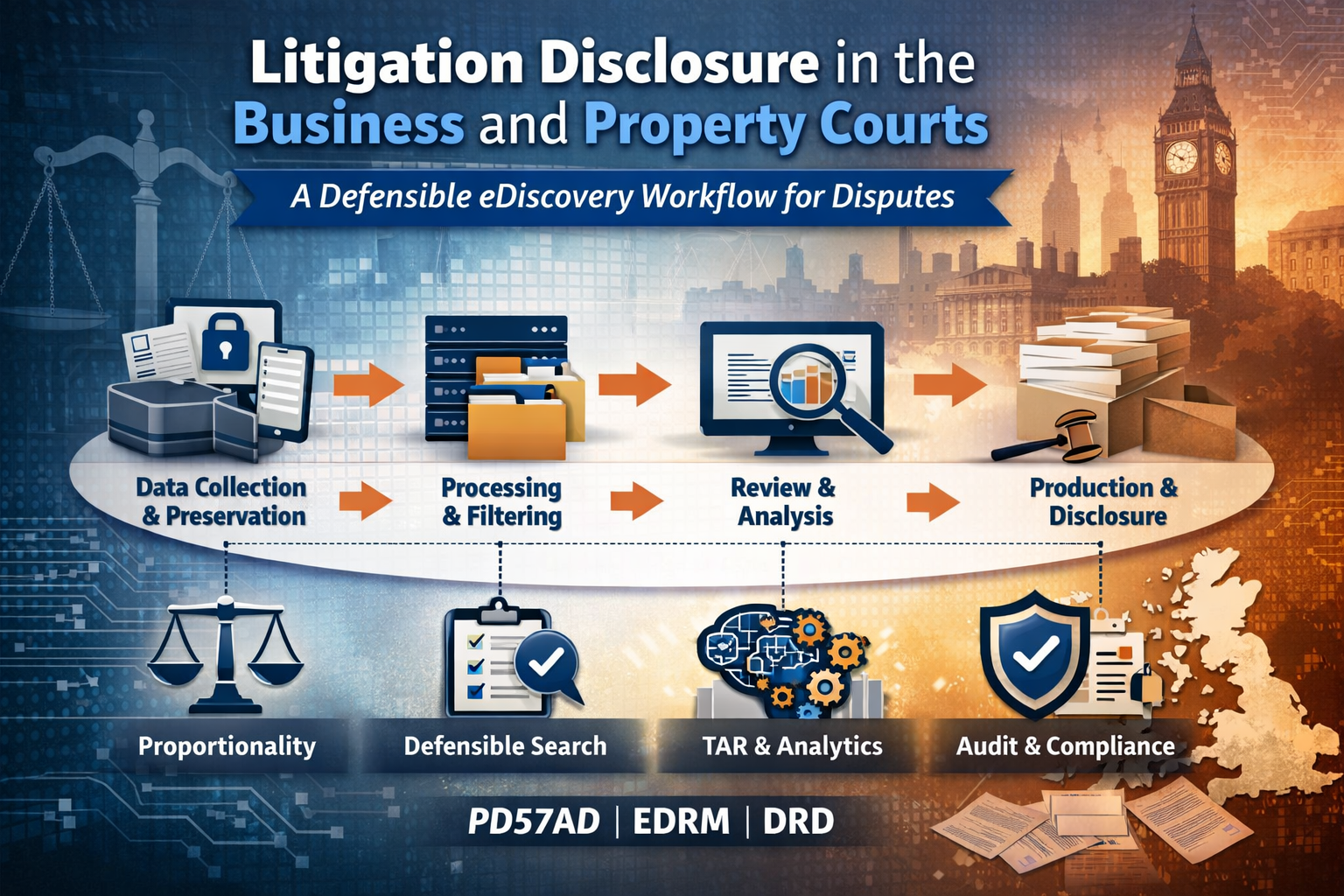
A structured eDiscovery workflow helps you meet the court’s proportionality expectations, protect defensibility (including chain of custody), and keep review and production aligned with case strategy rather than deadlines. [PD57AD; EDRM]. [1]
What the court expects under PD57AD
In the Business and Property Courts of England and Wales, Practice Direction 57AD (PD57AD) sets a disclosure framework built around what is reasonable and proportionate in the context of the issues. It does not apply in the County Court, and it contains specific carve-outs (so always confirm the applicable regime at the outset).
Two PD57AD duties matter operationally from day one. First, legal representatives must take reasonable steps to preserve relevant documents and to prevent deletion/destruction by agents or third parties; lawyers must notify the client of the preservation obligation and obtain written confirmation that the client has taken the required steps. Second, parties must disclose known adverse documents (unless privileged) regardless of whether an order for disclosure is made, and any search must be undertaken responsibly and conscientiously. These are not abstract duties: they are why early scoping and disciplined preservation are risk controls, not “nice-to-haves”.
PD57AD disclosure discussions are not meant to be tactical ambushes. The Disclosure Review Document (DRD) is expressly intended to facilitate focused discussions about the scope of Extended Disclosure, help parties agree a sensible and cost‑effective approach, and provide the court with proposals so the court can make appropriate case management decisions at the CMC. Where search-based models are in play, the DRD is the mechanism for identifying scope, limits, and cost. [DRD; PD57AD]. [2]
Why discovery becomes the bottleneck in practice
Most disclosure pain points are predictable—and avoidable—if you treat discovery as a managed workflow rather than a “document dump”.
Late scoping is the usual root cause. Teams assume the data picture (who the custodians are; where the documents sit; what platforms were used; what date ranges matter), then discover the reality only when deadlines get close. At that stage, every new repository becomes a cost shock and a timetable risk.
The second failure is review inflation. Without consistent processing, de‑duplication, and coherent grouping of related items (for example, email threads), lawyers re‑review the same content repeatedly in different guises. That is where cost and morale go to die—and where proportionality arguments become hard to sustain with a straight face.
The third failure is defensibility drift. If you cannot explain (and evidence) how you preserved data, what you searched, what you excluded, and why, you invite disputes about completeness and methodology. Under PD57AD, the point is not perfection; it is a process you can justify as responsible, conscientious, and proportionate to the issues.
A lawyer-friendly, defensible workflow mapped to EDRM
The EDRM model is useful because it describes eDiscovery as conceptual and iterative, not a rigid waterfall. You may loop back, refine, and repeat steps as your understanding evolves or as the pleadings and witness evidence sharpen the issues. That is exactly how real disputes progress. [EDRM]. [3]
A practical workflow that litigators can explain (to opponents, the court, and the client) usually looks like this:
Start with a data map, not a document dump. Identify likely repositories and custodians, capture the rationale (why these sources; why these date ranges), and set out what will be preserved. This is your foundation for proportionality because it demonstrates that you scoped by reference to issues and likelihood of probative value, rather than trawling blindly.
Preserve early, with chain of custody discipline. PD57AD requires reasonable preservation steps and written confirmation from the client. Practically, that means you want a record of what was preserved, when, how, and by whom—supported by repeatable protocols, integrity checks where appropriate, and an audit trail that reduces later argument about spoliation or incompleteness.
Process to reduce noise before you review. EDRM’s “volume triangle” concept captures a basic truth: you want the volume to come down as you move through the lifecycle. Normalisation, de‑duplication, and smart handling of communications are not “tech features”; they are how you convert a chaotic dataset into a review population that is proportionate, coherent, and auditable.
Treat search as a methodology, not a one-off keyword run. Where searches are required, document the approach: what you searched, why you searched it, what you excluded, and how you refined. That documentation becomes your defensibility narrative if there is a dispute later about scope or completeness.
Search, analytics, and TAR: speed, with defensibility safeguards
PD57AD explicitly anticipates the parties discussing and seeking to agree automated searches (including keyword and other automated searches), and the use of software or analytical tools—including technology assisted review (TAR)—with a view to reducing burden and cost. PD57AD also defines TAR broadly (including predictive coding and computer‑assisted review).
That said, the defensibility question is always the same: can you explain your protocol and validation? TAR and analytics can be powerful accelerators, but they do not remove the need for legal judgement, privilege controls, and quality assurance. A court-aligned approach generally includes (i) a clearly defined objective tied to Issues for Disclosure, (ii) transparent documentation of parameters and training/decision points, (iii) defensible sampling and validation, and (iv) escalation paths for edge cases (privilege, confidentiality, personal data).
This is also where “proportionality” becomes practical. You are not trying to review everything. You are trying to review what is reasonable in light of the issues, the likely existence of probative documents, and the cost and burden of retrieval and review. Analytics and TAR are often how you demonstrate that you took reasonable steps to reduce duplication and cost while still fulfilling disclosure obligations.
UK/EU realities: cross-border data and parallel scrutiny
For UK/EU practitioners, disclosure strategy increasingly sits alongside data protection constraints and cross-border handling decisions. Whatever your hosting or review model, you want a process that keeps control of access, audit trails, and decisions about transfer—so you can justify how you handled sensitive data while meeting litigation obligations.
Litigation also frequently runs in parallel with regulatory or internal investigations. For example, EU competition scrutiny can hinge on the same communications and transactional evidence that appears in civil proceedings: the European Commission describes Articles 101 and 102 TFEU as the central rules prohibiting anti-competitive agreements and abuse of dominance, and notes that cartels (including price-fixing and market sharing) are a “flagrant” example of illegal conduct. Even where your dispute is not a competition claim, parallel or related investigations can change evidence priorities overnight—another reason to keep a disciplined, searchable evidence record rather than a fragmented collection of exports.
Where Legal Tech Innovations supports litigators
Legal Tech Innovations supports disputes by combining experienced consultants with eDiscovery technology across each phase of the process—so litigators can keep disclosure proportionate, defensible, and aligned to strategy. The services are designed for legal disputes where organisations need to access, analyse, and present internal data as electronic evidence.
For disputes, two service elements tend to have the biggest immediate impact.
First, data acquisition and preservation: the team collects and safeguards evidence, using structured questioning and interviews to identify where data is stored and how it is held, supported by defined protocols that provide transparency over the process and sources collected (including email and mobile devices). That supports chain of custody and reduces later argument about “what was done”.
Second, workflow and platform support: LTI’s eDiscovery solutions can be accessed remotely via secure data centers in the UK and EU, with flexible engagement options (project-based and subscription models). That matters when you need to move quickly—without compromising access controls, audit trails, or review consistency.
Contact us to discover how LTI can help with your next mandate
info@legaltechinnovations.com | luke@legaltechinnovations.com